LTE security is an very important topic.
In LTE we have 3 key pillars of security. They are
1. Authentication
2. Integrity
3. Encryption.
1. Authentication:
1. The LTE network verifies the UE’s identity by challenging the UT (User Terminal) to use the keys and report the result.
2. The network checks the result against the expected
2. Integrity:
1. Signaling message receiver verifies that the received message is same as that has been transmitted.
2. This is done by using an integrity checksum.
3. It is used to guard against “man in the middle attack”.
4. MIMA is a way, where the attacker will intercept the message and modify the message and send it to the receiver. This can be eliminated.
3. Encryption:
1. The sender will encrypt the data with a key that is known be the receiver.
2. Only receiver will be able to decrypt the message.
3. This will help to guard against the hackers listening to the data.
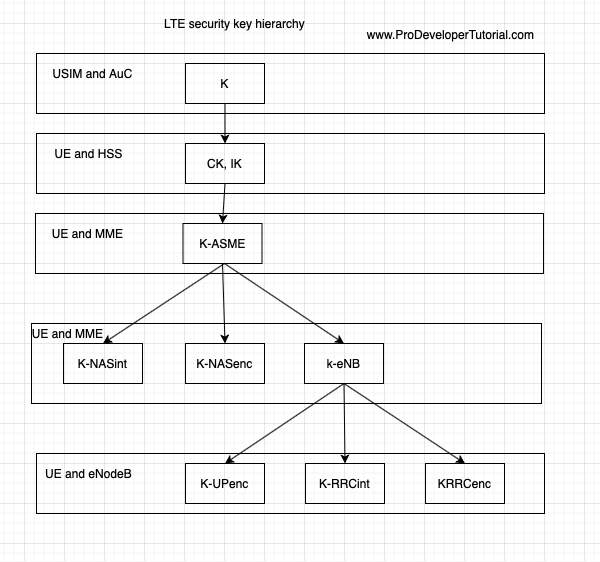
LTE security Hierarchy:
Below image shows the LTE security Hierarchy:
K key
K is the master key and it will be stored in SIM card and HSS/AuC.
K key is never transmitted.
All the other keys are derived from K key.
Length 128 bits
CK and IK
K key is used to derive Cipher key CK and Integrity key IK
Length: 128 bits
Derived from ‘K’ key
KASme [Access Security Management Entity]
With the help of CK and Ik, HSS and UE are able to derive KASme key
Length 256 bits
It is an intermediate key
KNASenc, KNASint
With KASme key, we are able to derive NAS and AS keys. i.e KNASenc, KNASint
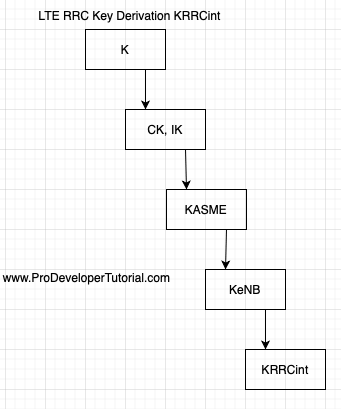
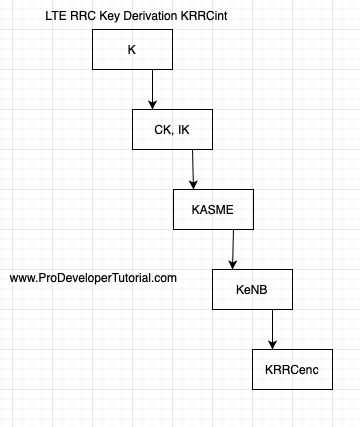
keNB
KeNB is a key derived by UE and MME from KASme during eNB handover.
KeNB should only be used for derivation of keys for RRC traffic and the derivation of keys for UP(User Plane) traffic or to derive transaction key KeNB during an eNB handover.
Length 256 bits
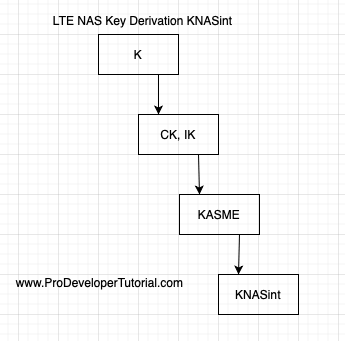
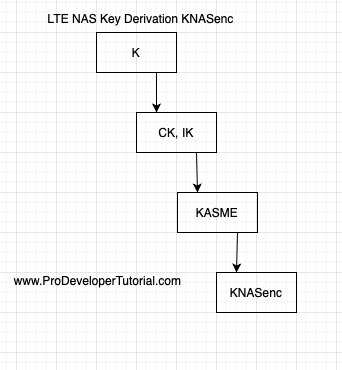
LTE NAS Key Derivation at the MME and UE
KNASint: Integrity protection key for NAS signaling messages
Length 256 bits
KNASenc: Encryption key for NAS signaling messages
Length 256 bits
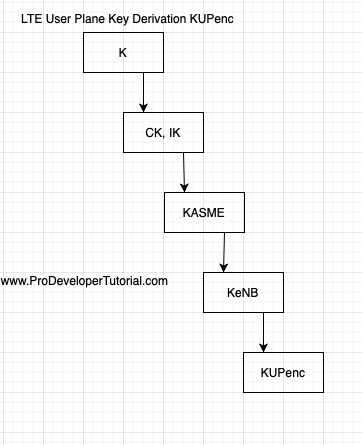
LTE User Plane Key Derivation at the eNodeB and UE
KUPenc:
Length 256 bits
LTE RRC Key Derivation at the eNodeB and UE
KRRCint: Integrity protection key for RRC signaling messages
Length 256 bits
KRRCenc: Encryption key for RRC signaling messages
Length 256 bits
3GPP security specification:
Below are the list of 3GPP defined security specifications for further reading:
LTE Security
• 33.401: System Architecture Evolution (SAE); Security architecture
• 33.402: System Architecture Evolution (SAE); Security aspects of non-3GPP
Lawful Interception
• 33.106: Lawful interception requirements
• 33.107: Lawful interception architecture and functions
• 33.108: Handover interface for Lawful Interception
Key Derivation Function
• 33.220: GAA: Generic Bootstrapping Architecture (GBA)
Backhaul Security
• 33.310: Network Domain Security (NDS); Authentication Framework (AF)
Relay Node Security
• 33.816: Feasibility study on LTE relay node security (also 33.401)
Home (e) Node B Security
• 33.320: Home (evolved) Node B Security