5G AKA procedure is required for UE to access the Network Services.
UE needs to be authenticated before it is connected to the network.
In 5G NR, IMSI has been replaced with SUCI (Subscription Permanent Identifier).
In LTE there were few instances where IMSI was sent in clear. This would have been an issue if anyone was listening.
In 5G NR this was fixed by using SUCI that replaces GUTI/TMSI/IMSI.
Confidentiality Algorithms in 3GPP Networks generally use MILENAGE, XOR & Comp128.
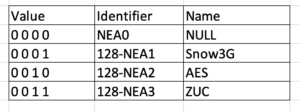
Below are few of Ciphering Algorithms.
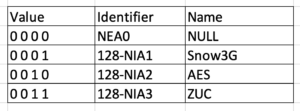
Below are some of the integrity algorithms.
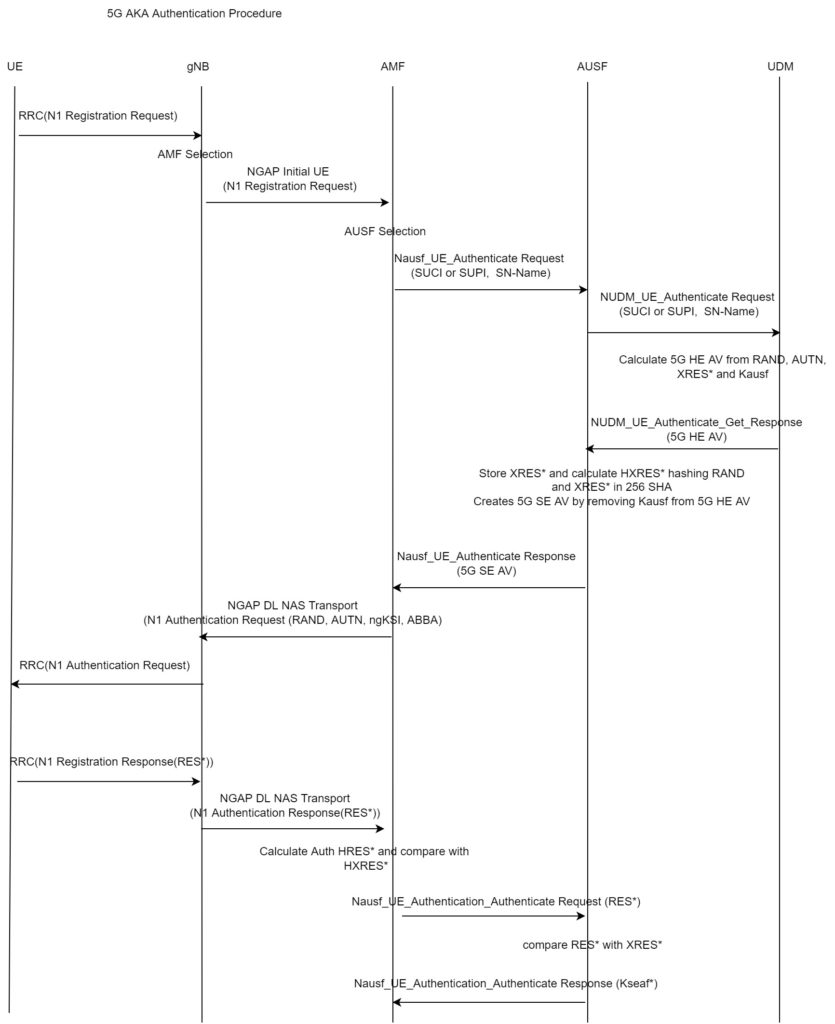
5G AKA Authentication Procedure
1. Authentication procedure starts when UE sends N1 registration request to RAN,
2. RAN will forward Initial UE request to AMF.
3. AMF will send Nausf_UEAuthentications Request with SUCI or SUPI and Serving network name to AUSF.
4. AUSF sends Nudm_UEAuthentication_Get Request with SUPI/SUCI to UDM.
5. UDM will use the algorithms to derive Kausf, MAC, XRES, CK, IK.
6. AUSF will derive 5G AV (Authentication Vector)
7. AMF Sends NAS Authentication Request to UE with RAND and AUTN from 5G SE AV
8. UE will use the authentication algorithms to derive XMAC, RES, CK, IK.
9. UE will then check the XMAC with MAC received in AUTN.
10. UE will derive RES then sends it to AMF.
11. AMF will calculate HRES from RES and it will compare HRES with HXRES that is received from AUSF.
12. AMF sends RES received from UE to AUSF with “Authenticate Request” message.
13. AUSF compares RES with the XRES received from UDM in step 5.
14. If it is successful, then AUSF sends Authentication Event notification to UDM with “Success”.